Isotopic Topology as a
Thermodynamically Unclonable Anchor
Throughput Asymmetry Constraints in Non-Equilibrium Metallic Gradients
The C4 Institute
ORCID: 0009-0001-7938-446X
The global semiconductor supply chain faces a critical vulnerability: counterfeit components and hardware trojans circumvent existing digital cryptographic protections. Current solutions, such as Silicon Physically Unclonable Functions (PUFs), rely on stochastic manufacturing variations that are susceptible to aging, thermal drift, and modeling attacks. This report introduces Isotopic Topology Authentication, a novel hardware assurance framework based on nuclear binding energy. By embedding non-equilibrium gradients of stable isotopes (e.g., 62Ni vs. 58Ni) within metallic interconnects, we create thermodynamically unclonable "Physical Anchors."
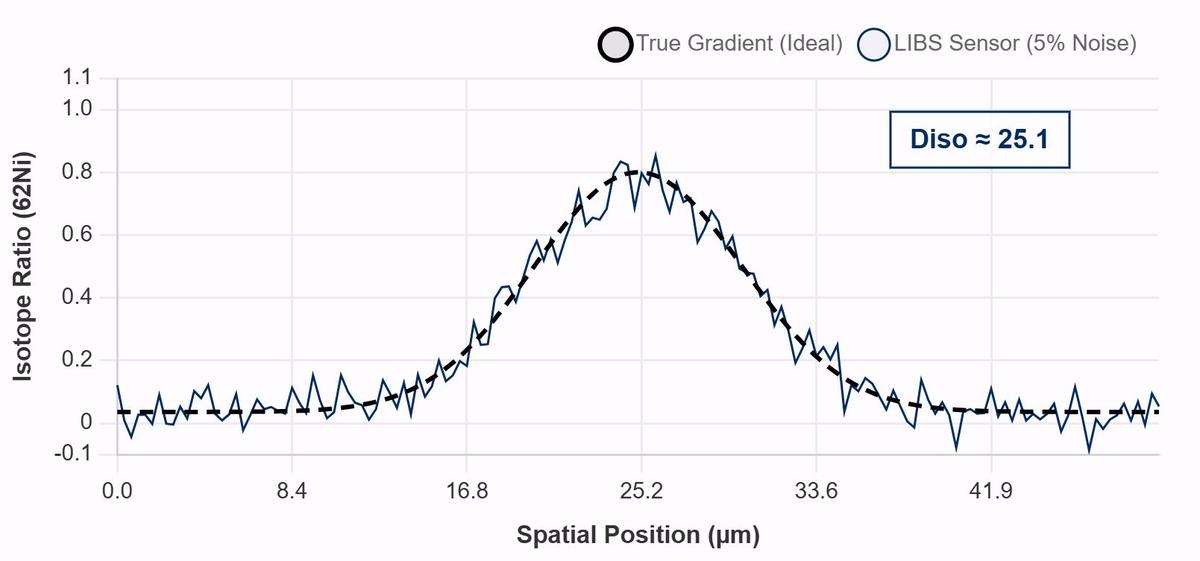
We demonstrate that while these gradients are chemically identical to standard interconnects, replicating the specific isotopic vector field requires atom-by-atom serial assembly. We quantify the resulting security barrier as a throughput asymmetry of 107, rendering cloning economically irrational. Simulation results confirm that these gradients are detectable via field-deployable Laser-Induced Breakdown Spectroscopy (LIBS) with a signal recovery confidence of >99% (Diso > 25.0) under 5% sensor noise.
The Physicochemical Gap
The integrity of the global semiconductor supply chain is increasingly compromised by the injection of counterfeit components, recycled die, and malicious hardware modifications. The economic impact is estimated at $7.5 billion annually, but the national security implications of compromised defense systems are incalculable.
Existing hardware assurance mechanisms rely primarily on electron transport phenomena. Current state-of-the-art solutions suffer from inherent trade-offs between stability, clonability, and detectability.
Vulnerability: ML modeling attacks; thermal drift
Vulnerability: Decoupled from die; swappable
Vulnerability: Destroyed at reflow (>260°C)
Vulnerability: None identified
Isotopic Fingerprinting
We introduce a method to encode information in the Isotopic Landscape of a material. Unlike standard doping, which alters chemical composition, this method alters the ratio of stable isotopes within a chemically pure metal.
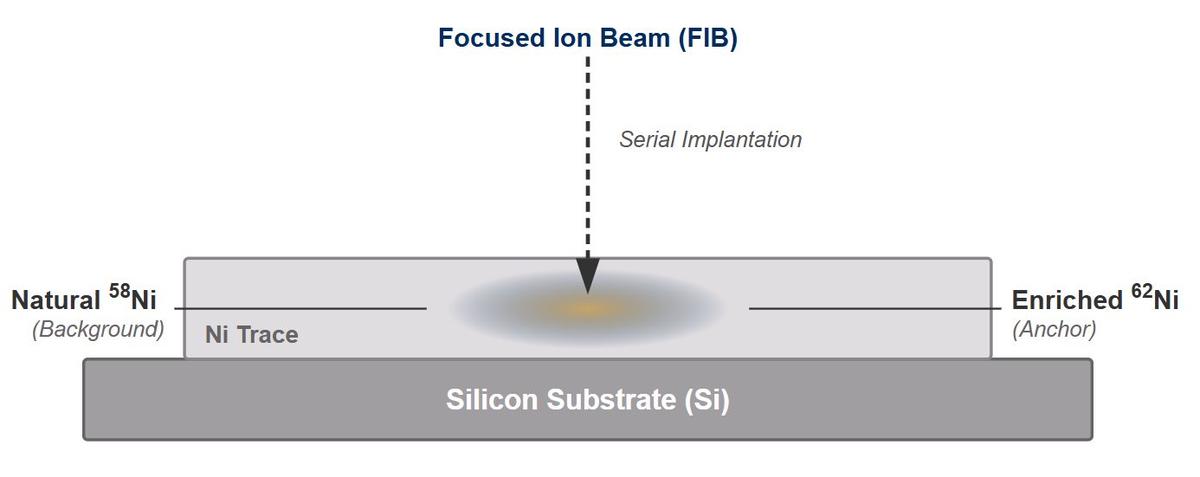
Standard metallization processes result in a homogeneous mix of isotopes based on terrestrial natural abundance (e.g., Nickel is nominally 68% 58Ni). Our approach utilizes Focused Ion Beam (FIB) implantation to create localized, non-equilibrium gradients where the concentration of a minority isotope (e.g., 62Ni) deviates significantly from the natural background.
To clone the tag, an adversary cannot simply use bulk alloy deposition. They must separate isotopes and deposit them with spatial precision matching the original gradient.
Legitimate batch time: <1 second per die
LIBS Signal Recovery Simulation
To validate the detectability of these gradients without laboratory-grade mass spectrometry, we simulated the spectral response of a portable Laser-Induced Breakdown Spectroscopy (LIBS) system.
We modeled the interaction of a 1064 nm pulsed laser (5 mJ) with the isotopic target: Silicon substrate with Ni metallization (62Ni peak: 80%), with a Gaussian noise floor of 5% applied to simulate thermal noise in a non-cooled CCD detector.
Sensor noise: 5% Gaussian
Result: Field verification feasible
The Depot-First Model
The physical permanence of Isotopic Topology suggests a "Depot-First" deployment model for high-assurance sectors. Rather than requiring verification at the end-user level, we propose implementation at logistics chokepoints (e.g., Defense Logistics Agency depots).
A benchtop LIBS unit screens 100% of incoming FPGA and ASIC inventory. To prevent damage to active circuitry, the tag is designed for placement on the package heat spreader or the scribe line of the die.
Isotopic Topology represents a paradigm shift in hardware assurance. By leveraging the immutable laws of nuclear physics, we establish a root of trust that is resistant to the cloning and aging vulnerabilities that plague electronic security primitives.
The calculated Throughput Asymmetry (106–107 seconds cloning time vs. <1 second legitimate) provides a robust economic barrier against counterfeiting, securing critical infrastructure against advanced persistent threats.
Future work focuses on empirical validation: fabrication of 62Ni gradients on silicon wafers and independent failure analysis to validate the 104-day cloning barrier.
Interested in Isotopic Topology
for Your Supply Chain?
Contact Baird Research to discuss pilot programs, technical partnerships, or licensing opportunities for defense and critical infrastructure applications.
